Products and Services
ProDNS
Large scale DNS server
We Focused on Performance, Security and Support with the Aim of Reducing Operating Costs that are too High for Overseas Products
ProDNS is a large-scale cache server such as ISP, cable TV, etc. developed by Nippon Cydnea with full scratch. We focused on performance, security and support with the aim of reducing operating costs that are too high for overseas products In addition, because of its feature and vulnerability that is easy to intrude, it tends to be attacked. There are two kinds of attack methods: DOS type and injection type, and ProDNS minimizes the effect of attack by taking various countermeasures.
Performance
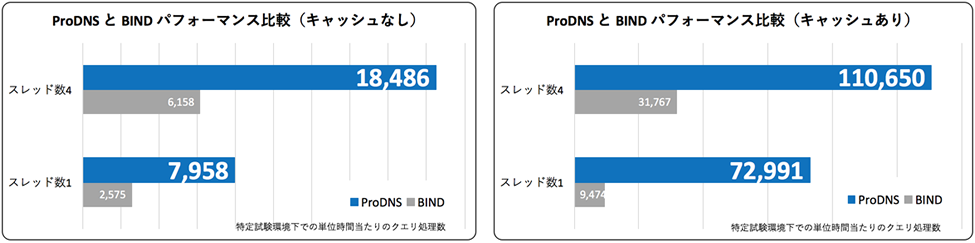
ProDNS is a simple structure that focuses on large systems that handle large numbers of DNS queries and implements only necessary functions. It simplifies the configuration and reduces operational costs. Beside narrowing down functions, it improves performance, and when compared with BIND, its processing power is 3 times to 7 times more (see paragraph).
Verification environment:
Authority server: CentOS 7.2, Intel Xeon E5645 2.4GHz, Core 1, Memory 2GB, HDD 20GB
・Cache server: CentOS 7.2, Intel Xeon E5645 2.4GHz, Core 4, Memory 2GB, HDD 20GB
・Client: CentOS 7.2, Intel Xeon E5645 2.4GHz, Core 1, Memory 2GB, HDD 20GB
Function · Security Measures
| Maximum values of various resources such as memory size, number of ports, number of connections, etc. can be set to prevent the operation from being unstable due to resource exhaustion even under high intensity. | |
| Access control | Connection refused setting is possible by setting in a range or individually the IP of the source that has unauthorized access or mass access. |
| Statistical information | Detailed statistical information can be obtained from the command line. You can also obtain statistical information via SNMP using Net-SNMP. |
| Security countermeasures(Slow query) | This is a problem when resources are exhausted due to the large amount of queries that take time to respond. ProDNS takes new requests even when the load is high by interrupting slow requests at a certain rate and processing new requests in priority. |
| Security countermeasures(Water torture) | It put a heavy load on the authority server by accessing to the same server which concentrated in a short period of time. After the authority server goes down, requests that can not return responses are accumulated in the cache server, and the cache server is also loaded. By setting Rate Limit, short-term requests to the same domain are restricted and the problem is solved. |
| Security countermeasures(Birthday Attack) | It is an attack which raises the entropy matching rate by sending the same request multiple times from the client. When multiple requests are sent, ProDNS deals with birthday attacks by collectively sending them to the authority server. |
| Security countermeasures(Entropy) | Increase entropy by randomizing the source port for authority with its own algorithm Security countermeasures(Transfer notifications injection) If the NS information of the authority from the parent authority server is cached in the setting, transfer notifications injection can be avoided by not overwriting the child's Authority NS information. (※Plan to implement) |
| Security countermeasures (ghost domain) | It is an attack that leaves impersonation information forcibly by preventing TTL run out of cache information of a specific domain. when acquiring an NS record that is the same as the cache from the authority server but different only in TTL, or when acquiring an NS record that is the same in cache and domain name but different only in RDATA, you can avoid ghost domains by using the shorter TTL of cache and acquired records. In addition, by giving an upper limit to the cache TTL, we try not to cache it for an unnecessarily long period. |
Recommended Environment
| OS | Linux(CentOS 6, 7 RedHat6, 7) For other Linux environments, please discuss more |
|---|---|
| Memory | 4GByte |
| CPU | Intel Xeon E5645 @ 2.4GHz 以上 |
| Other | Performance changes depending on the environment. For test version, please inquire. |
Supported RFC
Supporting RFC1034、1035、2181、2308、1123、6891、2671
Contact us
For further questions, requests for quotes, or any other inquiries please contact us now by clicking on the contact us box.

